More DOOM Madness
Tagged:Obscurantism
/
ϜΤΦ
Yet more DOOM madness, this distributing & installing the game via DNS.
Running DOOM Conventionally, But… Delivery/Installation, Not So Much
Incorrigible repeat readers of this Crummy Little Blog That Nobody Reads (CLBTNR) know that we’ve mentioned previously the craze of running the first-person shooter DOOM on unconventional platforms. The most recent instance was running it in a PDF file [1], apparently using an embedded scripting language.
Embedded scripting languages are, as a rule, evil. Data files and programs should be kept as separate as possible. Though, that’s often not very separate.
Today comes news that DOOM can be run on conventional hardware, but distributed, installed, and run by decidedly unconventional means:
 That’s pointing at an article on the blog of infrastructure and security engineer Adam
Rice. [2]
That’s pointing at an article on the blog of infrastructure and security engineer Adam
Rice. [2]
A bit of background:
-
DNS, or the Domain Name System, is an internet protocol that dates in its current from from RFC-1035 back in November of 1987. It’s a system for mapping host names for computers (like “www.someweekendreading.blog”) to IP addresses (things like “185.199.108.153”) that can actually be used to route network packets.
The data is stored on many computers world-wide.
-
DNS can also be used to distribute other kinds of data, mostly for normal purposes. Though, again as incorrigible CLBTNR readers know, it can be used to distribute silly things as well, like the lyrics to the “Bad Horse” song in Dr. Horrible’s Sing-Along Blog. [3]
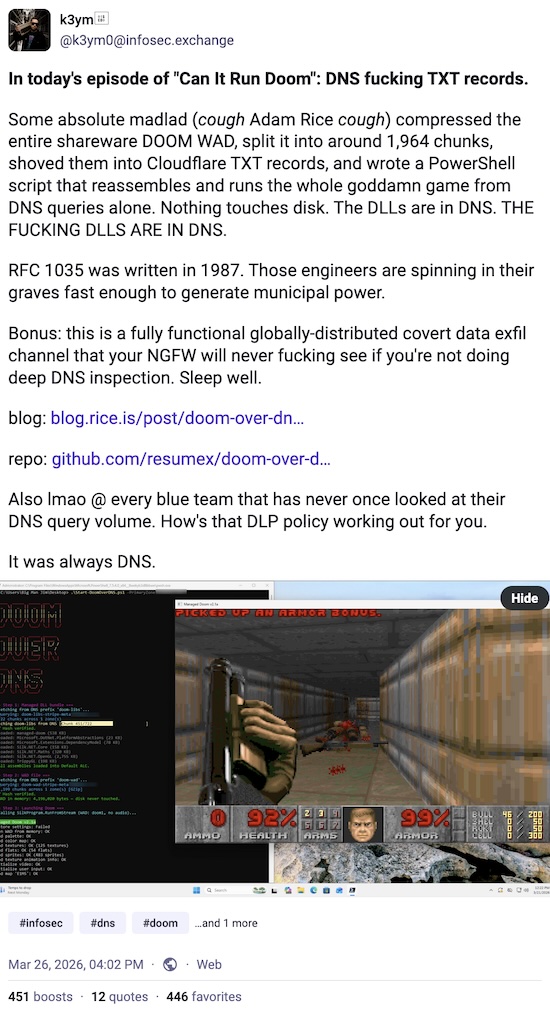
Rice is a fan of using DNS to poke security holes in networks:
If you’ve ever poked at one of my CTF challenges, you’ve probably noticed a pattern - I love hiding payloads in TXT DNS records. I stash the malicious code in a TXT record, have the implant query for it at runtime, and now suddenly the payload is being delivered by the same infrastructure that resolves
grandmas-cookie-recipes.com. It’s trivially easy to set up and surprisingly annoying to catch forensically, because who’s flagging the historic contents of TXT records?
If you’re familiar with the ways of computer-touchers, you can pretty much write the rest of the story. For everybody else, here’s what he did:
The universal benchmark for “can this thing do something it was never designed to do?” is, always has been, and always will be DOOM. Thermostats run DOOM, pregnancy tests run DOOM, and I want DNS to run DOOM.
- He found a C# port of DOOM. C# can be run on things called managed .NET assemblies.
It’s not important exactly what that is, except for 2 facts:
- They’re on almost all reasonably recent Windows machines, and are not too uncommon on Linux and Mac machines. So there’s wide availability.
- The “managed” part means bytes can be loaded from a stream to the net, and no data ever need touch a file on a tightly controlled corporate disk.
Ok, so you divide the C# DOOM binaries into about 2,000 pieces of about 2,000 characters each, given them serial numbers for reassembly in the correct order, and upload them as part of the DNS info for a host you control.
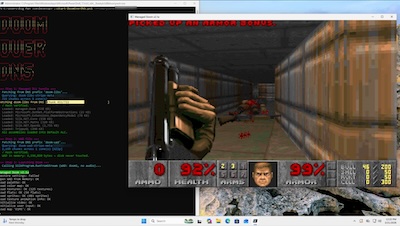 Result: A script tiny enough to be typed from memory can “download” DOOM from the DNS
system, evading most network security on hosts where DOOM has no business, and be played
on a computer which is supposed to be game-free.
Result: A script tiny enough to be typed from memory can “download” DOOM from the DNS
system, evading most network security on hosts where DOOM has no business, and be played
on a computer which is supposed to be game-free.
Rice’s description:
I described this project to my mother as such: It’s like taking a phone book and playing the 1986 academy award winning action film Top Gun starring Tom Cruise as a flip-book animation out of the phone numbers on every page.
 Within minutes, the de rigeur meme appeared, as shown here. (Is that always a Cuban
flag patch on the shoulder of the astronaut with the gun?)
Within minutes, the de rigeur meme appeared, as shown here. (Is that always a Cuban
flag patch on the shoulder of the astronaut with the gun?)
Reaction, in the Mastodon toot above, was swift to point out that this is an excellent malware vector and data exfiltration channel, since nobody does this kind of deep inspection on DNS traffic on corporate networks.
Counter-reaction, this being Mastodon, was equally swift and informative:
- In the old news file, people mentioned this has been done since the late 80s, sometimes chat programs written by the very engineers who wrote IETF-1035. People have even done voice encoding, for (bad quality) audio calls via DNS. So as security holes go, this is well known and probably blocked?
- Most corporate networks don’t let people query DNS directly, but only to the corporate DNS server that is an internal cache. OTOH, that internal DNS server often just relays queries it doesn’t already know to an outside server, so it might work. In practice, exfiltration of corporate data like this is apparently a famous sales demo used by security vendors.
- “Reasonable” network security (DNS logs, a well built forwarding chain, a properly tuned dashboard, iodine) will detect this sort of mishegoss within seconds. Also, most organizations do not have “reasonable” network security of that sort, even impressively large organizations. (See above using DNS data exfiltration as a sales demo for security vendors.)
The Weekend Conclusion
Computer security is just about impossible. Things can always be suborned into doing stuff they were not designed to do, and in fact are absolutely not supposed to do.
I have no useful advice. Sometimes ya just gotta bear witness to the high weirdness.
(Ceterum censeo, Trump incarceranda est!)
Notes & References
1: Weekend Editor, “DOOM Runs On… What?!”, Some Weekend Reading blog, 2025-Jun-30. ↩
2: A Rice, “Can it Resolve DOOM? Game Engine in 2,000 DNS Records”, Rice’s blog, 2026-Mar-21. ↩
3: Weekend Editor, “DNS: An Improbable Medium for Humor”, Some Weekend Reading blog, 2024-May-02. ↩
Gestae Commentaria
Comments for this post are closed pending repair of the comment system, but the Email/Twitter/Mastodon icons at page-top always work.